Experts en Applications Web. Agence web à Montréal-Est.
Prositeweb mets sa passion au service de votre succès en vous offrant des solutions digitales innovantes et personnalisées. Faites confiance à notre savoir-faire pour propulser votre présence en ligne vers de nouveaux sommets.
Agence web montréal – Nos services en développement web et applications
Nous decomplexions les concepts technologiques pour votre faire gagner en temps et argent

Bienvenue sur le site web de votre Agence web à Montréal-Est experte en site web et applications.
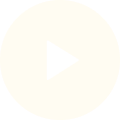
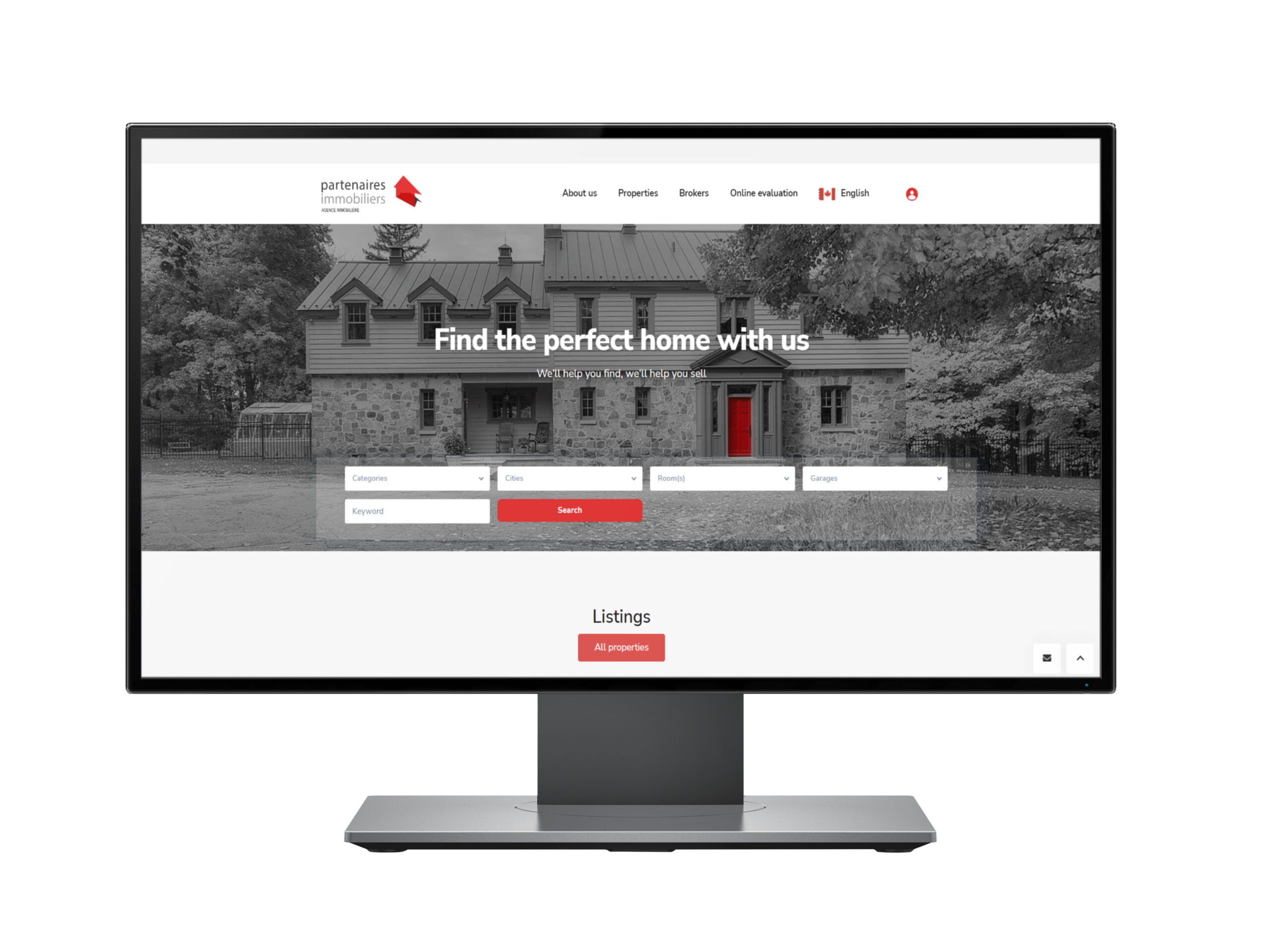
Nous sommes une agence web à Montréal-Est, offrant à notre clientèle un éventail de services en la conception de site web, création de boutiques en ligne, développement d’applications d’entreprise.
Fondée en 2015, notre mission consiste à fournir aux entreprises des solutions clés en main à des prix compétitifs. Nous nous démarquons par notre expertise avancée en programmation et notre capacité à surpasser les défis technologiques.
Si vous êtes à la recherche d’une équipe pour un partenariat à long terme, où la technologie ne représente jamais un obstacle, veuillez nous contacter.
Ce que les clients disent de nous
Gabriel Labelle
Très bon service de la part de Gilblas. Il est très à l'écoute et très professionnel avec ses clients.
Edgard You
Pour avoir travaillé avec Prositeweb et Gilblas pendant quelques mois, je recommande celle-ci grâce à sa réactivité et son expertise en développement/Full Stack/Magento.
Martin Beaudet
Début 2024, nous avons travaillé avec Prositeweb, Gilblas et ce fût un véritable plaisir et succès. Ça se résume en suivi, communication et compétence. C'est ce qu'on recherche lorsqu'on confie un mandat web (API) personnalisé comme le nôtre. Chapeau, Prositeweb, Gilblas, je le recommande et je retravaillerai avec sans aucun doute.
Julie Levesque
Nous travaillons avec Prositeweb pour l'amélioration de l'un de nos sites web et nous sommes très satisfaits.
Questions fréquemment posées (FAQ)
Quels services Prositeweb offre-t-elle ?
Prositeweb est spécialisée dans la création de site web, le développement de boutiques en ligne, et la conception d’applications d’entreprise. Notre agence se consacre à la transformation digitale des visions de nos clients en solutions web sur mesure, performantes et autonomes.
Quelle est la philosophie de Prositeweb ?
Notre philosophie est de fournir des solutions web entièrement sur mesure. Chaque projet est considéré comme unique, et nous nous engageons à développer des solutions personnalisées qui concrétisent à 100 % la vision de nos clients, tout en minimisant la dépendance à des ressources externes.
Comment votre Agence web à Montréal-Est intègre-t-elle l’innovation dans ses projets ?
Prositeweb se distingue par l’utilisation de minicodes, des ressources conçues en interne qui permettent d’intégrer des fonctionnalités à vos projets de manière rapide et adaptable. Cette approche assure une livraison efficace et une adaptabilité sans pareil à vos besoins.
Qu’est-ce qui fait la force de l’équipe de Prositeweb ?
Notre équipe est notre plus grande force. Dynamique et dotée d’une expertise pointue en solutions web, nous transcendons les limitations technologiques pour proposer des solutions qui dépassent les attentes. Notre maîtrise multidimensionnelle de la programmation web nous permet d’offrir une vaste gamme de services.
Depuis quand votre Agence web à Montréal-Est existe-t-elle et quelle est sa mission ?
Fondée en 2015, la mission de Prositeweb est de fournir aux entreprises des solutions clés en main à des prix compétitifs. Nous visons à surmonter les défis technologiques avec notre expertise avancée en programmation, se démarquant ainsi dans notre domaine.
Prositeweb est-elle ouverte à des partenariats à long terme ?
Oui, Prositeweb cherche à établir des partenariats à long terme avec ses clients, où la technologie ne représente jamais un obstacle. Si vous recherchez une équipe dédiée capable de surmonter tout défi technologique, veuillez nous contacter pour discuter de votre projet.
Est-ce que vous developpez des modules?
Prositeweb est une Agence web à Montréal-Est qui a également de l’expertise en développement des modules. Nous avons eu l’occasion de créer des plugins que vous trouverez sur le site web WordPress.org. Sur notre page solution, vous verrez aussi quelques modules.